January 31, 2026
The Silent Cyber Threat Most People Ignore

Roshan Ali R
Author
Phishing is one of the most common and dangerous cyber threats today. Unlike advanced hacking techniques that exploit software vulnerabilities, phishing attacks exploit human trust. A single careless click on a fake link or message can expose your passwords, personal data, financial details, and even give attackers complete control over your online accounts.
Phishing attacks are increasing rapidly because they are easy to execute and highly effective. Many victims do not realize they have been attacked until their accounts are compromised or money is stolen.
Why Phishing Attacks Are So Effective
Phishing works because attackers understand human psychology. Messages are crafted to create urgency, fear, or excitement, forcing users to act quickly without verifying the source. These messages often appear to come from trusted organizations such as banks, payment apps, social media platforms, delivery services, or government agencies.
Common tricks include fake account suspension warnings, refund notifications, prize offers, or security alerts demanding immediate action.
Common Types of Phishing Attacks
Email Phishing
Attackers send fake emails pretending to be from legitimate companies. These emails contain malicious links or attachments designed to steal login credentials or install malware.
Smishing (SMS Phishing)
Scam messages are sent via SMS claiming account issues, prize winnings, or urgent verification requests. Clicking the link usually leads to a fake website.
Vishing (Voice Phishing)
Attackers make phone calls posing as bank officials or customer support agents and trick victims into revealing sensitive information such as OTPs, PINs, or card details.
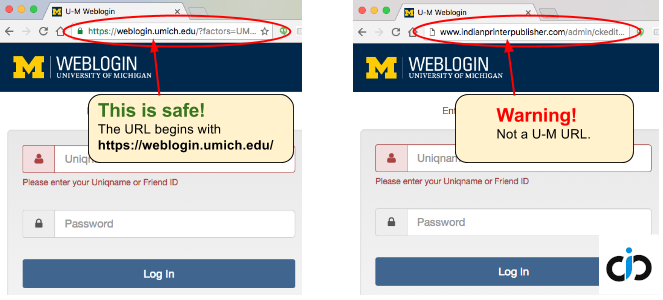
Fake Login Pages
Cybercriminals create websites that look identical to real ones. Once users enter their login details, the information is captured and misused.
Warning Signs of a Phishing Attempt
Be alert if you notice urgent or threatening language, spelling or grammar mistakes, unknown sender addresses, suspicious links, or requests for passwords, OTPs, or PINs. Legitimate organizations never ask for sensitive information through messages, emails, or phone calls.
How to Protect Yourself from Phishing Attacks
Never click on suspicious or unexpected links. Always verify the sender before responding. Carefully check website URLs before logging in. Enable two-factor authentication wherever possible. Use strong and unique passwords for different accounts. Delete and report phishing emails or messages immediately.
Extra Safety Tips for Mobile Users
Avoid installing apps from unknown links. Never share OTPs with anyone. Use official apps instead of browser links. Keep your phone and apps updated. Enable spam filters and call-blocking features.
Final Thoughts
Phishing attacks succeed not because users are careless, but because attackers are skilled at deception. Awareness is the strongest defense against phishing. Taking a few seconds to verify before clicking can protect you from financial loss, identity theft, and long-term digital damage.
Remember: One careless click is all it takes to compromise your entire digital life.
Phishing attacks are increasing rapidly because they are easy to execute and highly effective. Many victims do not realize they have been attacked until their accounts are compromised or money is stolen.
Why Phishing Attacks Are So Effective
Phishing works because attackers understand human psychology. Messages are crafted to create urgency, fear, or excitement, forcing users to act quickly without verifying the source. These messages often appear to come from trusted organizations such as banks, payment apps, social media platforms, delivery services, or government agencies.
Common tricks include fake account suspension warnings, refund notifications, prize offers, or security alerts demanding immediate action.
Common Types of Phishing Attacks
Email Phishing
Attackers send fake emails pretending to be from legitimate companies. These emails contain malicious links or attachments designed to steal login credentials or install malware.
Smishing (SMS Phishing)
Scam messages are sent via SMS claiming account issues, prize winnings, or urgent verification requests. Clicking the link usually leads to a fake website.
Vishing (Voice Phishing)
Attackers make phone calls posing as bank officials or customer support agents and trick victims into revealing sensitive information such as OTPs, PINs, or card details.
Fake Login Pages
Cybercriminals create websites that look identical to real ones. Once users enter their login details, the information is captured and misused.
Warning Signs of a Phishing Attempt
Be alert if you notice urgent or threatening language, spelling or grammar mistakes, unknown sender addresses, suspicious links, or requests for passwords, OTPs, or PINs. Legitimate organizations never ask for sensitive information through messages, emails, or phone calls.
How to Protect Yourself from Phishing Attacks
Never click on suspicious or unexpected links. Always verify the sender before responding. Carefully check website URLs before logging in. Enable two-factor authentication wherever possible. Use strong and unique passwords for different accounts. Delete and report phishing emails or messages immediately.
Extra Safety Tips for Mobile Users
Avoid installing apps from unknown links. Never share OTPs with anyone. Use official apps instead of browser links. Keep your phone and apps updated. Enable spam filters and call-blocking features.
Final Thoughts
Phishing attacks succeed not because users are careless, but because attackers are skilled at deception. Awareness is the strongest defense against phishing. Taking a few seconds to verify before clicking can protect you from financial loss, identity theft, and long-term digital damage.
Remember: One careless click is all it takes to compromise your entire digital life.
